Imagine you’re sending a letter to a friend. Before it reaches their mailbox, it needs a clear address, right? Well, think of the internet like a vast network of digital mailboxes. To ensure your digital “letters” (data) reach their destination, they need something similar to a mailing address – that’s where IP addresses come in.
IP stands for Internet Protocol, but let’s keep it simple: it’s like the internet’s version of a home address. Just as your home address tells the mail carrier where to deliver your letter, an IP address directs data packets to their intended recipients across the internet.
So, what is an IP address? It’s a unique identifier assigned to every device connected to the internet, whether it’s your smartphone, computer, or smart fridge. This address helps computers communicate with each other, allowing you to browse websites, send emails, stream videos, and more. Without IP addresses, the internet as we know it wouldn’t function.
What is the history of IP addresses?
The history of IP addresses traces back to the early development of the internet. In the 1960s and 1970s, researchers and engineers laid the groundwork for what would eventually become the modern internet.
One of the fundamental concepts in this was the idea of packet switching, which involved breaking down data into smaller packets for transmission across various interconnected nodes. To ensure that these packets reached their intended destinations accurately, a method for uniquely identifying each device on the network was needed. This gave rise to the concept of the Internet Protocol (IP) address.
The development of IP addressing protocols began in the late 1970s and early 1980s, with the creation of IPv4. IPv4 introduced a 32-bit address space, allowing for approximately 4.3 billion unique addresses.
However, as the internet continued to expand exponentially, it became evident that IPv4’s address space would soon be exhausted. In response to this crisis, the Internet Engineering Task Force (IETF) developed IPv6 (Internet Protocol version 6) in the late 1990s, which offered a vastly expanded address space of 128 bits, capable of accommodating an almost unimaginable number of unique addresses.
How do IP addresses work?
Here’s the elaboration of how do ip addresses work –
# Basics of IP routing
When you send data over the internet, it’s broken down into small packets. IP routing is like the postal system for these packets, where data packets are sent from one device to another. Each packet contains information about its destination, allowing routers to decide where to send it next.
# DHCP (Dynamic Host Configuration Protocol)
DHCP is like a digital leasing office for IP addresses. It automatically assigns IP addresses to devices on a network, making it easier to manage and ensuring each device gets a unique address without manual configuration.
When a device connects to a network, it sends a request to the DHCP server. This server then assigns it an IP address from a pool of available addresses.
# NAT (Network Address Translation)
NAT is like a translator for internet addresses. It allows devices within a local network to share a single public IP address.
It works by assigning each device within the local network a private IP address. When these devices send data out to the internet, the NAT router translates their private IP addresses to the single public IP address before sending it onto the wider internet. This allows for efficient use of public IP addresses and enables multiple devices to access the internet simultaneously.
What is the Role of IP Addresses in Internet Communication?
Here are a few roles that IP addresses play in facilitating online interactions –
- Domain names: Websites are typically identified by domain names (like www.example.com), but behind the scenes, each domain name corresponds to an IP address. When you type a domain name into your web browser, your device uses DNS to translate that domain name into the corresponding IP address, allowing it to connect to the correct web server.
- DNS (Domain Name System) resolution: DNS is like the internet’s phone book, translating human-readable domain names into machine-readable IP addresses.
- SMTP (Simple Mail Transfer Protocol): SMTP is the protocol used for sending email messages over the internet. When you send an email, your email client communicates with an SMTP server, which then uses the recipient’s email address to determine the destination mail server’s IP address. This IP address is used to deliver the email to the correct server for onward delivery to the recipient.
- Network Identification: IP addresses serve as unique identifiers for devices within a network, allowing routers and other network devices to accurately route data packets to their intended destinations.
- Peer-to-Peer Communication: In peer-to-peer networks, such as file-sharing networks or online gaming platforms, IP addresses are used to establish direct connections between individual devices.
- Quality of Service (QoS) Control: Some network protocols and systems use IP addresses to prioritize traffic based on factors such as bandwidth requirements, latency sensitivity, or security considerations, ensuring optimal performance for critical applications or services.
- Geolocation and Content Delivery: IP addresses can be used to determine the geographic location of a device or user. It allows content providers to deliver localized or region-specific content and services.
- Network Security: IP addresses play a crucial role in network security by enabling access control lists (ACLs), firewall rules, and intrusion detection systems to monitor and regulate network traffic based on source and destination IP addresses.
- Virtual Private Networks (VPNs): IP addresses are used in VPNs to create secure and private connections over the internet.
- IP Telephony (VoIP): IP addresses facilitate voice communication over the internet through protocols like Voice over Internet Protocol (VoIP). Devices use IP addresses to establish connections for voice calls, enabling services like Skype, Zoom, and other internet-based telephony systems.
- Internet of Things (IoT): With the proliferation of IoT devices, IP addresses are essential for enabling communication and connectivity between smart devices, sensors, and other IoT endpoints. Each IoT device is assigned a unique IP address, allowing them to exchange data and interact with other devices and services over the internet.
What is IPv4 and IPv6?
IPv4 and IPv6 are indeed two different versions of the Internet Protocol (IP) that define how devices are addressed on a network. Now, let’s talk about both in detail –
IPv4 (Internet Protocol version 4) addresses are a numerical label assigned to each device connected to a computer network that uses the Internet Protocol for communication. It employs a 32-bit address scheme, allowing for approximately 4.3 billion unique addresses, which were thought to be more than sufficient during its inception.
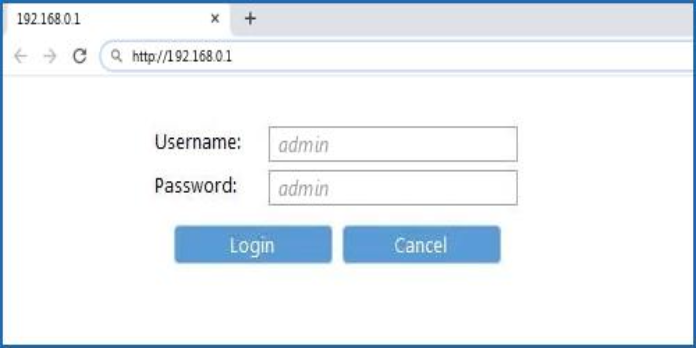
These are typically written in dotted-decimal notation, consisting of four decimal numbers separated by periods (e.g., 192.168.0.1). Each decimal number represents 8 bits of the address, making up a total of 32 bits.
IPv6 (Internet Protocol version 6) addresses are the successor to IPv4, designed to address the limitations of IPv4’s address space. It uses a 128-bit address scheme, offering an almost limitless supply of unique addresses, totaling approximately 340 undecillion (3.4 × 10^38).
These are represented as eight groups of four hexadecimal digits separated by colons (e.g., 2001:0db8:85a3:0000:0000:8a2e:0370:7334)
Advantages of IPv6 over IPv4 are –
It offers significantly more unique addresses and includes built-in security features such as IPsec, enhancing data protection. Its simplified header structure enables faster routing and processing of packets. It also provides better support for emerging technologies like IoT (Internet of Things) and 5G networks.
What are the types of IP addresses?
There are two main ways to categorize IP addresses: by their location and accessibility (public vs. private), and by their assignment method (static vs. dynamic).
On the Basis of Accessibility
On the basis of accessibility, IP addresses are divided into two parts – public and private.
Public IP addresses are like the street addresses of devices on the internet, visible to anyone accessing the web, while private IP addresses are more like room numbers within a building, known only to devices within the local network.
Here’s a table differentiating between public and private IP addresses:
| Aspect | Public IP Address | Private IP Address |
| Visibility | Visible to the entire internet | Limited to the local network |
| Assignment | Assigned by ISPs | Assigned by network administrators |
| Purpose | Identifies devices on the internet | Identifies devices within a local network |
| Accessibility | Accessible from anywhere on the internet | Not directly accessible from the internet |
| Security Concerns | Prone to external threats and hacking attempts | Generally more secure since they’re not visible externally |
| Examples | Assigned to websites, servers, routers, etc. | Assigned to computers, smartphones, printers, etc. |
On the Basis of Assignment Method
IP addresses are divided into Static IP Address and Dynamic IP address on the basis of their assignment method.
A static IP address is manually configured and remains constant over time. A dynamic IP address is automatically assigned to a device by a DHCP server.
Here’s a table highlighting the differences between both IP addresses:
| Aspect | Static IP Address | Dynamic IP Address |
| Configuration | Manually configured by the network administrator | Automatically assigned by a DHCP server |
| Stability | Remains constant over time | Can change over time as devices connect/disconnect |
| Assignment | Assigned to a specific device | Assigned dynamically to devices as needed |
| Management | Requires manual configuration and updates | Managed automatically by DHCP server |
| Use Cases | Commonly used for servers, printers, routers, and other network devices requiring a consistent address | Suitable for devices like computers, smartphones, and tablets in residential or small business networks |
| Remote Access | Ideal for remote access and hosting services | May require additional configurations for remote access due to changing addresses |
| Predictability | Provides predictable addressing for specific devices | Addresses may change, requiring dynamic DNS or other methods for consistency |
| Network Efficiency | Less efficient for dynamic environments where devices frequently connect/disconnect | Provides efficient allocation of addresses and reduces address exhaustion |
How to Find Your IP Address?
The process of finding your ip address is a breeze. But the steps you need to follow vary from device to device. So follow them accordingly.
# Using Command Prompt (Windows)
Open Command Prompt by typing in “cmd” in the Start menu. Type “nslookup” followed by the domain name or hostname you want to look up, then press Enter.
The command prompt will display the corresponding IP address(es) associated with the domain name or hostname.
# Using Terminal (Mac)
Open Terminal by looking for it in Spotlight. The second option is that you can navigate to Applications > Utilities > Terminal.
Type “nslookup” followed by the domain name or hostname you want to look up, then press Enter. Then the Terminal will display the corresponding IP address(es).
# Using Online Tools
There are several websites and online tools that allow you to look up IP addresses by entering a domain name or hostname.
Examples include websites like WhatIsMyIPAddress.com, IPinfo.io, and DNSstuff.com.
# Using Built-in Network Utilities
Most operating systems have built-in network utilities that allow you to look up IP addresses.
On Windows, you can use the “ping” command followed by the domain name or hostname to retrieve the IP address.
On Mac, you can use the “ping” command in Terminal in a similar way.
# Check Network Settings
You can also find the IP address of your own device by checking its network settings.
On Windows, go to Settings > Network & Internet > Ethernet or Wi-Fi, then click on the network connection to view its properties.
On Mac, go to System Preferences > Network, then select the active network connection to view its IP address.
By following these methods, you can easily look up for your IP address.
IP Address Security and Privacy Concerns
Here are some common IP address security threats and their implications:
- IP Address Spoofing:
IP address spoofing involves forging the source IP address to conceal the identity of the sender or impersonate another entity.
Attackers can use IP address spoofing to bypass access controls, launch distributed denial-of-service (DDoS) attacks, or conduct reconnaissance without being detected.
- IP Address Scanning and Enumeration:
Attackers use automated tools to scan and enumerate IP addresses to identify vulnerable systems, open ports, or services running on network devices.
Scanning techniques such as port scanning, network mapping, and service enumeration help attackers gather information about target networks and potential entry points for exploitation.
- IP Address Hijacking:
IP address hijacking involves unauthorized takeover of IP addresses belonging to legitimate entities, often through exploitation of vulnerabilities in routing protocols or unauthorized changes to DNS records.
Attackers can do so to intercept or redirect traffic intended for the legitimate owner, enabling eavesdropping, man-in-the-middle attacks, or data interception.
4. IP Address Tracking and Profiling:
IP address tracking involves monitoring and recording the online activities associated with specific IP addresses to create user profiles, track browsing behavior, or deliver targeted advertising.
IP address tracking raises privacy concerns, as it can infringe on individuals’ rights to anonymity, confidentiality, etc.
5. Tracking:
Every device connected to the internet has a unique IP address, which can be used to trace the device’s location, internet service provider (ISP), and sometimes even the specific user.
Websites, advertisers, and even cybercriminals can use this information to monitor online activities, track browsing habits, and potentially identify individuals.
How to Protect Your IP Address?
Protecting and hiding your IP address is essential for safeguarding your online privacy and security. Here are several effective strategies to help you achieve this:
- Use a Virtual Private Network (VPN)
A VPN masks your IP address and provides anonymity online. Choose a reputable VPN service provider with a strict no-logs policy to ensure that your browsing activities remain private.
Then, enable it whenever you connect to the internet, especially when accessing public Wi-Fi networks or engaging in sensitive online activities.
- Use a Proxy Server
Proxy servers hide your IP address and routing your requests through their own IP addresses.
Unlike VPNs, these may not provide encryption or offer the same level of security and privacy protection, so choose carefully and ensure the proxy server you use is trustworthy.
- Tor (The Onion Router)
Tor is a free and open-source software that anonymizes your internet traffic by routing it through nodes. It encrypts your data multiple times and passes it through several relays, making it difficult for anyone to trace your online activities back to your IP address.
- Use Encrypted Messaging and Email Services
Opt for encrypted messaging apps and email services that prioritize user privacy and security by encrypting your communications end-to-end.
- Use Secure and Privacy-Focused Browsers
Consider using privacy-focused browsers like Mozilla Firefox or Brave, which offer built-in features to enhance online privacy and security, such as tracking protection and anti-fingerprinting measures.
- Avoid Clicking on Suspicious Links
Be cautious when clicking on links in emails, social media posts, or websites, as they may lead to phishing sites or malware-infected pages that could compromise your IP address and personal information.
Final Words
IP addresses are like digital IDs for devices on the internet. They’re super important because they help devices talk to each other. Without them, the internet wouldn’t work.
But, IP addresses can give away a person’s location, which isn’t always safe. That’s why some people use VPNs to hide their IP addresses and stay safe online.
In short, IP addresses are crucial for internet communication, but they can also pose privacy risks.
Related Posts: